Technology is designed to make life easier: to automate processes, save time, and reduce human effort.But behind every line of code is a human, and

Since participating in the Techwomen…

I sometimes find myself with burning topics to write about, at times I develop such articles and then before I publish, my security mind tells
Everybody looks forward to the birth of a baby in a family, we want to know what gender the baby is, the complexion, the size,

Two days ago, I was in the bank to make withdrawals using the Automated Teller Machine, (ATM) located in the bank premises. The queue was

CertNexus Cyber Secure Coder™ (CSC) is the comprehensive certification for validating secure coding practices – for all developers, in all programming languages, on all platforms.

From June 5th – 7th 2018, I attended the InfosecurityEurope 2018 held at the Olympia in London: Europe’s Number 1 Information security event. The 3-day

I bought a new Dell Laptop with 8Gb RAM and 512 Hard Disk, 2.2Hz processor speed and I saw myself returning it back to the
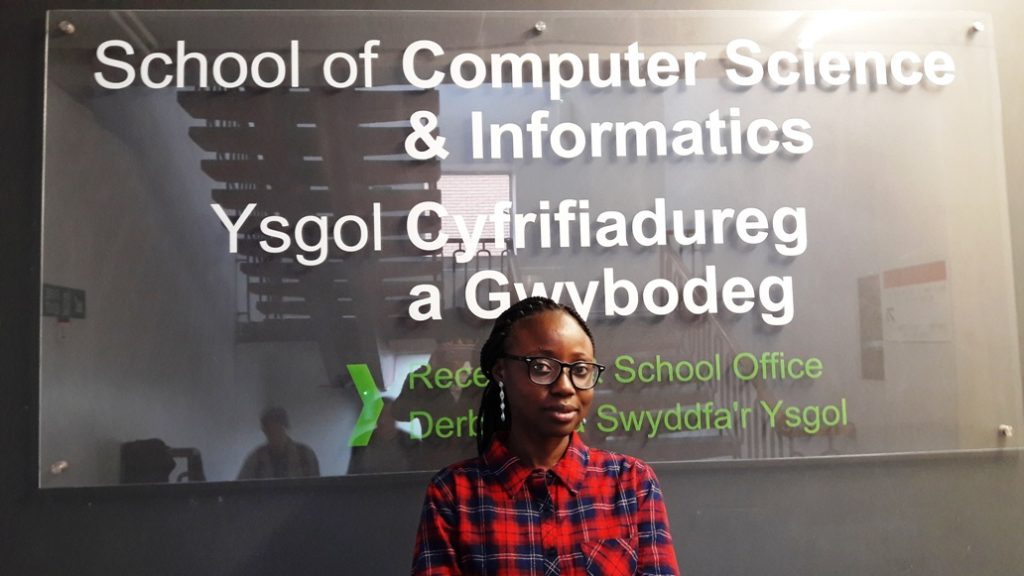
And so, I begin another journey in the field of cyber security… June this year 2017, I had the rare opportunity to be #SelectedForChevening scholarship
It is no doubt that Innovations are fueled by technology which in turn is the bedrocks of development in any society. Last month, I participated